
Krawl
Krawl is a cloud-native web honeypot and deception server. It creates realistic fake web applications with low-hanging vulnerabilities and decoy data to detect and track malicious activity from attackers and crawlers. Includes a real-time monitoring dashboard.
Services
Krawl
A modern, cloud-native web honeypot and deception server designed to detect, delay, and analyze malicious activity from attackers, web crawlers, and automated scanners. It creates realistic fake web applications to attract and identify suspicious behavior.
What You Can Do After Deployment
- Visit your domain — the honeypot server starts serving deceptive pages immediately
- Access the dashboard — go to your domain followed by the dashboard secret path shown in the logs to monitor activity
- View real-time data — watch incoming requests, detected attackers, and suspicious patterns
- Export reports — download activity logs and analysis data for your security team
- Customize traps — configure deception pages, response delays, and canary tokens via environment variables
Key Features
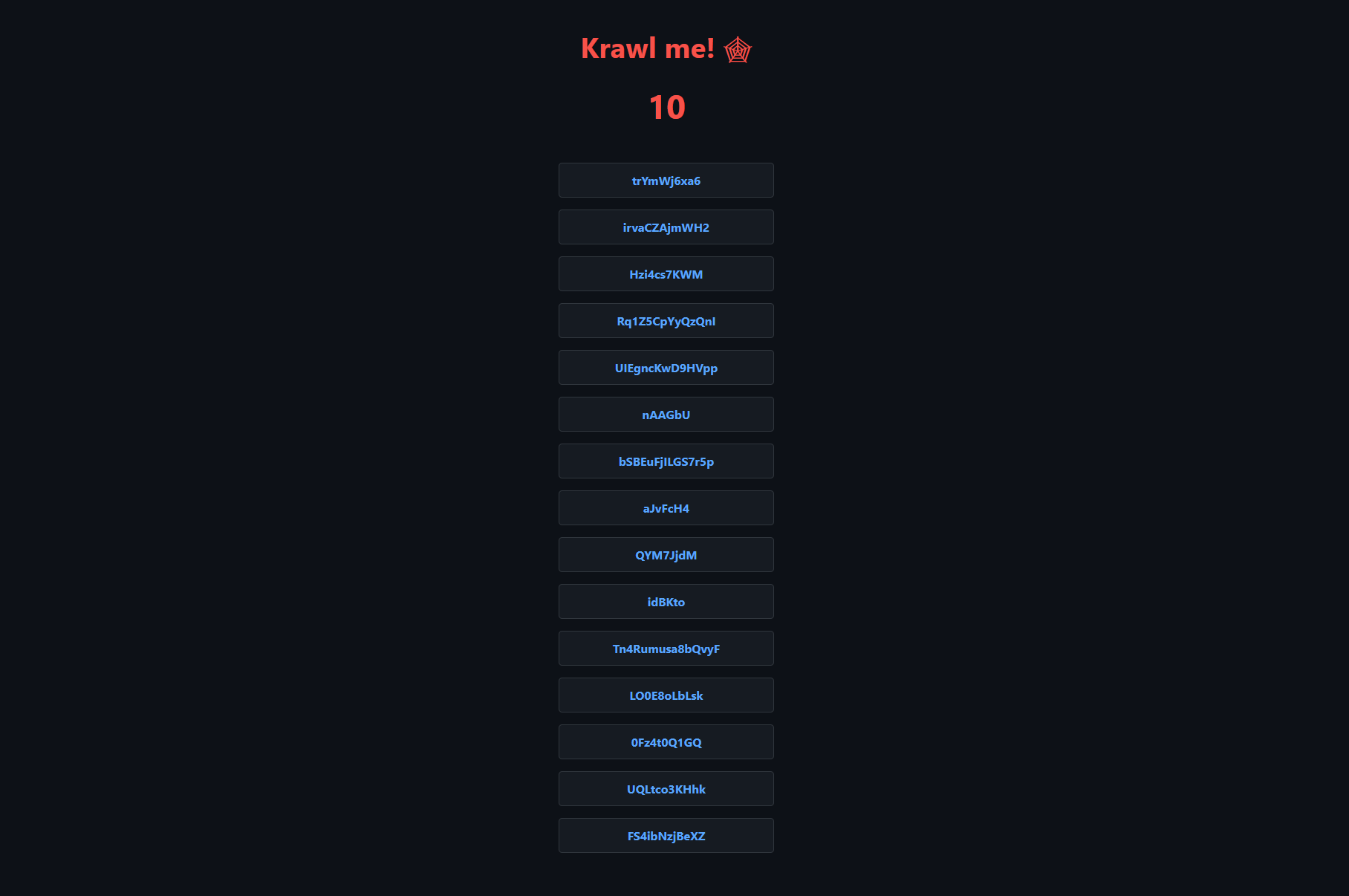
- Spider trap pages with infinite random links to waste crawler resources
- Fake login pages (WordPress, phpMyAdmin, admin panels)
- Honeypot paths advertised in robots.txt to catch scanners
- Fake credentials — realistic usernames, passwords, and API keys
- Canary token integration for external alerts
- Real-time monitoring dashboard with IP reputation analysis
- Automatic attacker detection and analysis
- SQLite database with configurable data retention
- Configurable response delays to slow down attackers
Default Login
The dashboard path and password are auto-generated on first start. Check the container logs to find them, or set them via the environment variables KRAWL_DASHBOARD_SECRET_PATH and KRAWL_DASHBOARD_PASSWORD.
License
MIT — GitHub